 Librería Perelló (Valencia)
Librería Perelló (Valencia)
 Librería Aciertas (Toledo)
Librería Aciertas (Toledo)
 El AlmaZen del Alquimista (Sevilla)
El AlmaZen del Alquimista (Sevilla)
 Librería Elías (Asturias)
Librería Elías (Asturias)
 Librería Kolima (Madrid)
Librería Kolima (Madrid)
 Donde los libros
Donde los libros
 Librería Proteo (Málaga)
Librería Proteo (Málaga)
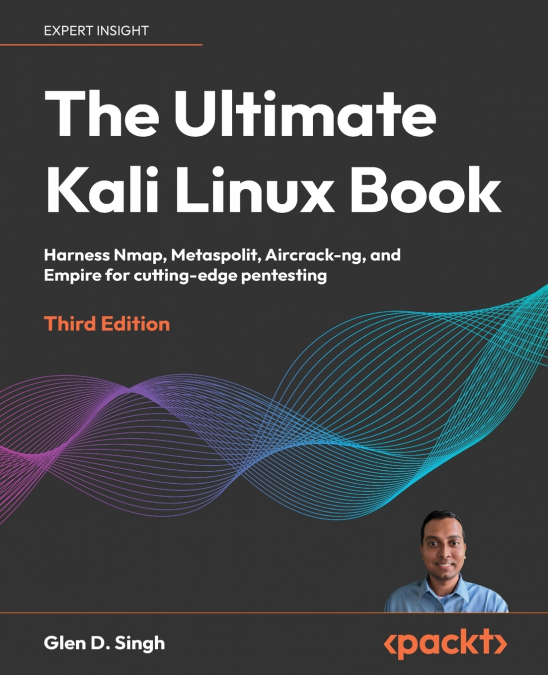
Excel in penetration testing by delving into the latest ethical hacking tools and techniques from scratchPurchase of the print or Kindle book includes a free eBook in PDF format.Key Features- Learn to think like an adversary to strengthen your cyber defences- Execute sophisticated real-life penetration tests, uncovering vulnerabilities in enterprise networks that go beyond the surface level- Securely manipulate environments using Kali Linux, ensuring you’re fully equipped to safeguard your systems against real-world threatsBook DescriptionEmbark on an exciting journey into the world of Kali Linux - the central hub for advanced penetration testing. Honing your pentesting skills and exploiting vulnerabilities or conducting advanced penetration tests on wired and wireless enterprise networks, Kali Linux empowers cybersecurity professionals.In its latest third edition, this book goes further to guide you on how to setup your labs and explains breaches using enterprise networks. This book is designed for newcomers and those curious about penetration testing, this guide is your fast track to learning pentesting with Kali Linux 2024.x. Think of this book as your stepping stone into real-world situations that guides you through lab setups and core penetration testing concepts. As you progress in the book you’ll explore the toolkit of vulnerability assessment tools in Kali Linux, where gathering information takes the spotlight. You’ll learn how to find target systems, uncover device security issues, exploit network weaknesses, control operations, and even test web applications.The journey ends with understanding complex web application testing techniques, along with industry best practices. As you finish this captivating exploration of the Kali Linux book, you’ll be ready to tackle advanced enterprise network testing - with newfound skills and confidence.What you will learn- Establish a firm foundation in ethical hacking- Install and configure Kali Linux 2024.1- Build a penetration testing lab environment and perform vulnerability assessments- Understand the various approaches a penetration tester can undertake for an assessment- Gathering information from Open Source Intelligence (OSINT) data sources- Use Nmap to discover security weakness on a target system on a network- Implement advanced wireless pentesting techniques- Become well-versed with exploiting vulnerable web applicationsWho this book is forThis pentesting book is for students, trainers, cybersecurity professionals, cyber enthusiasts, network security professionals, ethical hackers, penetration testers, and security engineers. If you do not have any prior knowledge and are looking to become an expert in penetration testing using the Kali Linux, then this book is for you.Table of Contents- Introduction to Ethical Hacking- Building a penetration testing lab- Setting up for Advanced Penetration Testing Techniques- Passive Reconnaissace- Exploring Open Source Intelligence- Active Reconnaissance- Performing Vulnerability Assessments- Understanding Network Penetration Testing- Performing Network Penetration Testing- Post-Exploitation Techniques- Delving into Command and Control Tactics- Working with Active Directory Attacks- Advanced Active Directory Attacks- Advanced Wireless Penetration Testing- Social Engineering Attacks- Understanding Website Application Security- Advanced Website Penetration Testing- Best Practices for the Real World- Appendix