 Librería Perelló (Valencia)
Librería Perelló (Valencia)
 Librería Aciertas (Toledo)
Librería Aciertas (Toledo)
 El AlmaZen del Alquimista (Sevilla)
El AlmaZen del Alquimista (Sevilla)
 Librería Elías (Asturias)
Librería Elías (Asturias)
 Librería Kolima (Madrid)
Librería Kolima (Madrid)
 Donde los libros
Donde los libros
 Librería Proteo (Málaga)
Librería Proteo (Málaga)
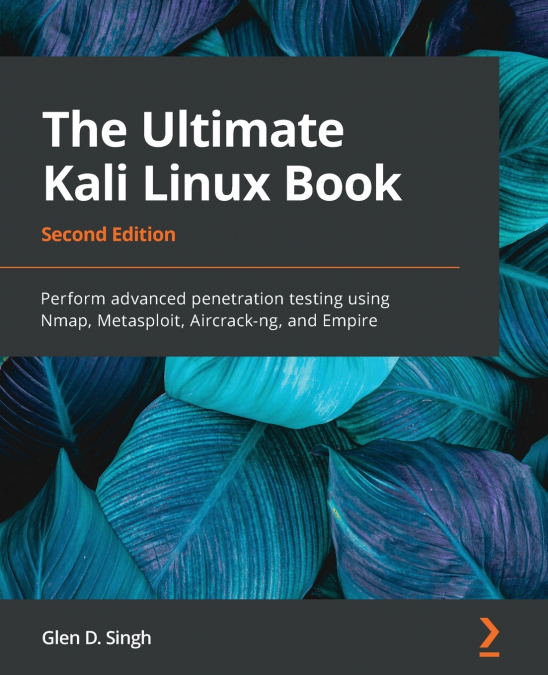
The most comprehensive guide to ethical hacking and penetration testing with Kali Linux, from beginner to professionalKey FeaturesLearn to compromise enterprise networks with Kali LinuxGain comprehensive insights into security concepts using advanced real-life hacker techniquesUse Kali Linux in the same way ethical hackers and penetration testers do to gain control of your environmentPurchase of the print or Kindle book includes a free eBook in the PDF formatBook DescriptionKali Linux is the most popular and advanced penetration testing Linux distribution within the cybersecurity industry. Using Kali Linux, a cybersecurity professional will be able to discover and exploit various vulnerabilities and perform advanced penetration testing on both enterprise wired and wireless networks.This book is a comprehensive guide for those who are new to Kali Linux and penetration testing that will have you up to speed in no time. Using real-world scenarios, you’ll understand how to set up a lab and explore core penetration testing concepts. Throughout this book, you’ll focus on information gathering and even discover different vulnerability assessment tools bundled in Kali Linux. You’ll learn to discover target systems on a network, identify security flaws on devices, exploit security weaknesses and gain access to networks, set up Command and Control (C2) operations, and perform web application penetration testing. In this updated second edition, you’ll be able to compromise Active Directory and exploit enterprise networks. Finally, this book covers best practices for performing complex web penetration testing techniques in a highly secured environment.By the end of this Kali Linux book, you’ll have gained the skills to perform advanced penetration testing on enterprise networks using Kali Linux.What you will learnExplore the fundamentals of ethical hackingUnderstand how to install and configure Kali LinuxPerform asset and network discovery techniquesFocus on how to perform vulnerability assessmentsExploit the trust in Active Directory domain servicesPerform advanced exploitation with Command and Control (C2) techniquesImplement advanced wireless hacking techniquesBecome well-versed with exploiting vulnerable web applicationsWho this book is forThis pentesting book is for students, trainers, cybersecurity professionals, cyber enthusiasts, network security professionals, ethical hackers, penetration testers, and security engineers. If you do not have any prior knowledge and are looking to become an expert in penetration testing using the Kali Linux operating system (OS), then this book is for you.Table of ContentsIntroduction to Ethical HackingBuilding a Penetration Testing LabSetting Up for Advanced Hacking TechniquesReconnaissance and FootprintingExploring Active Information GatheringPerforming Vulnerability AssessmentsUnderstanding Network Penetration TestingPerforming Network Penetration TestingAdvanced Network Penetration Testing - Post ExploitationWorking with Active Directory AttacksAdvanced Active Directory AttacksDelving into Command and Control TacticsAdvanced Wireless Penetration TestingPerforming Client-Side Attacks - Social EngineeringUnderstanding Website Application SecurityAdvanced Website Penetration TestingBest Practices for the Real World